Hi,
I am new here and I hope this is the right place for this thread.
I just started to play around with Kali-Linux and its WiFi tools.
So I took two wireless routers, I had at home and started playing around with tools like airodump-ng, wifite, airgeddon.
I use an Alfa AR9271 as wireless adapter.
So here is my problem/question:
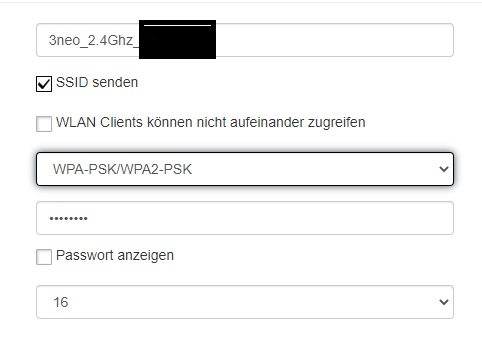
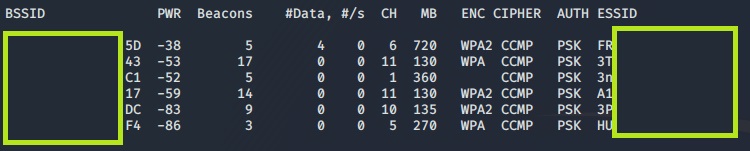
As long as my ZTE router is configured to use WPA-PSK/WPA2-PSK (I think that means WPA+WPA2 ?!?), all tools used on Kali, either display an empty/blank field for the encryption method or doesn't display my network at all. If I try to attack my network with wifite, it says "no attacks available".
Every other wireless network displays WPA, WPA2... in the ENC column.
In my router settings i can choose between "WPA-PSK/WPA2-PSK" and "WPA2(AES)-PSK". With "WPA2(AES)-PSK" everthing works fine, the problem only occurs with "WPA-PSK/WPA2-PSK.
My network ist the third from top. There is also a neighbour's network that acts exactly the same. (not on the screenshot)
I hope someone can tell me what is happening here.
Greetings!
I am new here and I hope this is the right place for this thread.
I just started to play around with Kali-Linux and its WiFi tools.
So I took two wireless routers, I had at home and started playing around with tools like airodump-ng, wifite, airgeddon.
I use an Alfa AR9271 as wireless adapter.
So here is my problem/question:
As long as my ZTE router is configured to use WPA-PSK/WPA2-PSK (I think that means WPA+WPA2 ?!?), all tools used on Kali, either display an empty/blank field for the encryption method or doesn't display my network at all. If I try to attack my network with wifite, it says "no attacks available".
Every other wireless network displays WPA, WPA2... in the ENC column.
In my router settings i can choose between "WPA-PSK/WPA2-PSK" and "WPA2(AES)-PSK". With "WPA2(AES)-PSK" everthing works fine, the problem only occurs with "WPA-PSK/WPA2-PSK.
My network ist the third from top. There is also a neighbour's network that acts exactly the same. (not on the screenshot)
I hope someone can tell me what is happening here.
Greetings!

