TCP challenge ack limit is a numebr to limit the sending packets of challenge ack per second. The implementation is:
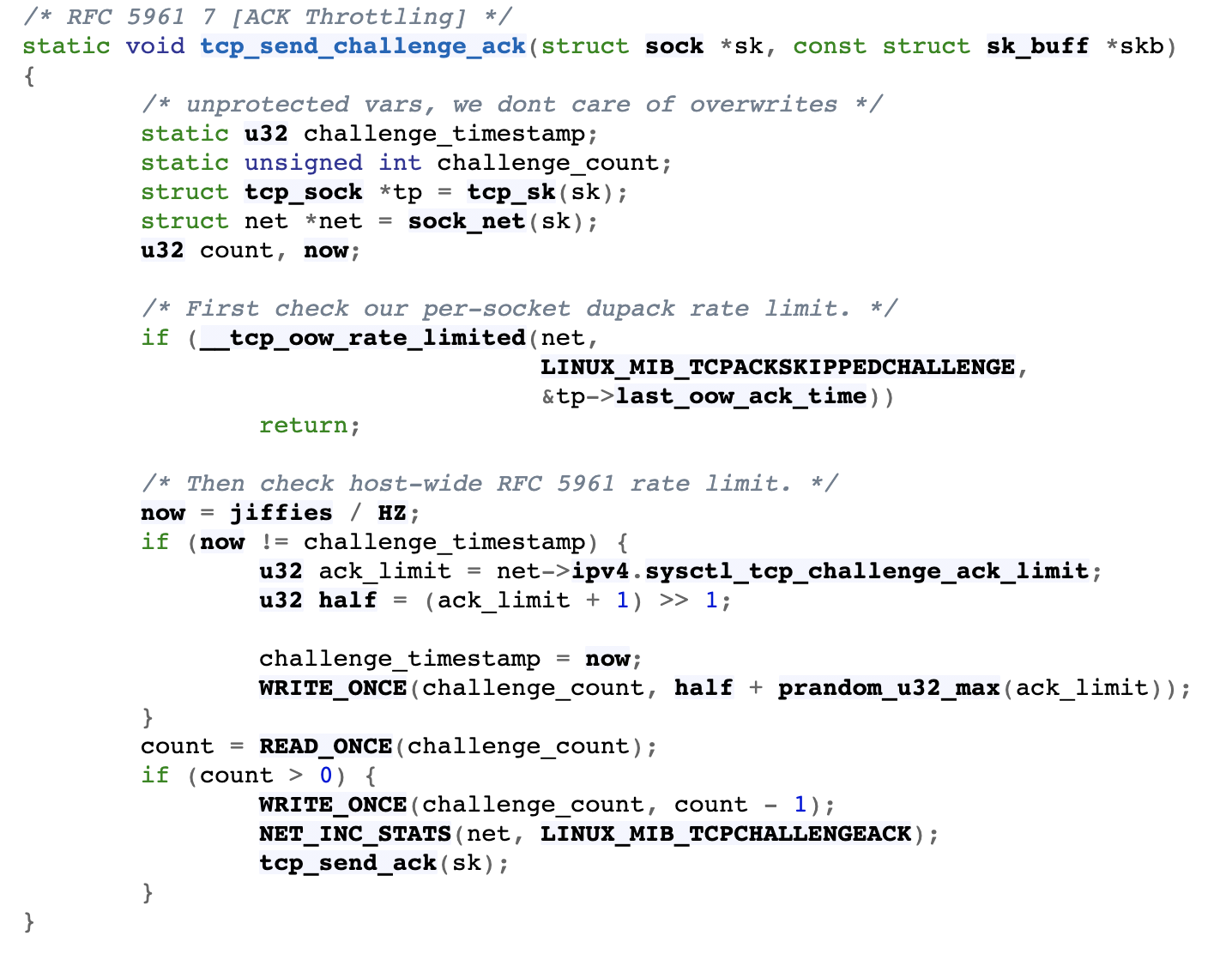
To solve the problem in the paper Off-Path TCP Exploits: Global Rate Limit Considered Dangerous, the global challenge count is randomized. And I want to know why the seed of function prandom_u32_max is set to ack_limit, a fixed number, and if the seed is timestamp will be better. Thanks.
To solve the problem in the paper Off-Path TCP Exploits: Global Rate Limit Considered Dangerous, the global challenge count is randomized. And I want to know why the seed of function prandom_u32_max is set to ack_limit, a fixed number, and if the seed is timestamp will be better. Thanks.


