J
Jarret W. Buse
Guest
Metasploit Installation
Metasploit is a penetration tool used to test vulnerabilities on systems in a network. Weak areas on the network are found so you can fix the security issues before a hacker can find them and exploit them.
Metasploit can be found at http://downloads.metasploit.com/data/releases/metasploit-latest-linux-installer.run. Once downloaded, you need to give it executable priveleges. You can then install it by running it as root with the command “sudo ./metasploit-latest-linux-installer.run”.
NOTE: You can also download Metasploit from http://www.rapid7.com/products/metasploit/download.jsp and receive the product key as well.
The screen should appear like Figure 1. To continue with the install, click the “Forward” button.
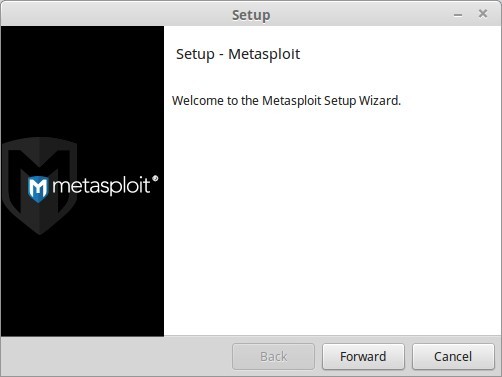
FIGURE 1
Next, look over the License Agreement, as shown in Figure 2, and select “I accept the agreement” and then click the “Forward” button.
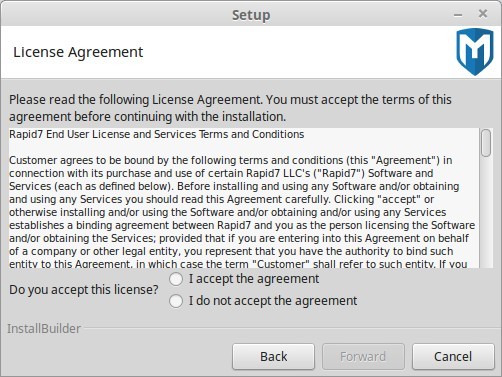
FIGURE 2
The next window allows you to set the destination folder for the installation. The default is /opt/metasploit as seen in Figure 3. Change it if needed or accept the default and then press the “Forward” button.
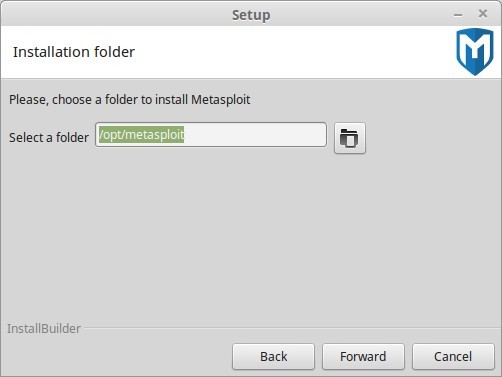
FIGURE 3
The next screen prompts you to allow Metasploit to be run as a service. The service will automatically start when the system loads. Select “Yes” to accept the program to be run as a service or “No” if you want to start it manually. To start the service manually, type “sudo service metasploit start” in a terminal. Once done, select “Forward” to continue.
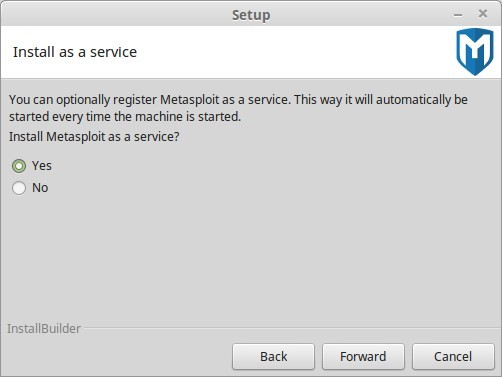
FIGURE 4
The next window alerts you to disable any Antivirus software and Firewall applications. The window is seen in Figure 5. Click the “Forward” button when you have read over the information.
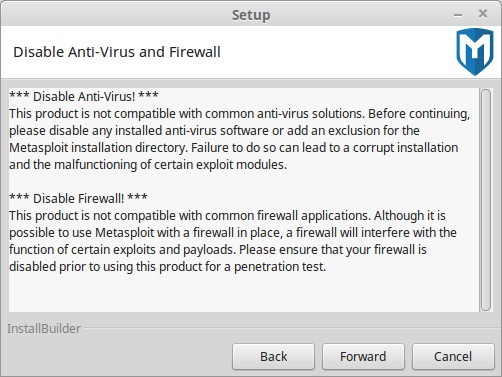
FIGURE 5
The next screen prompts you to enter an SSL Port for metasploit to use. The default is 3790 as shown in Figure 6. Set the port number as you desire and click the “Forward” button.
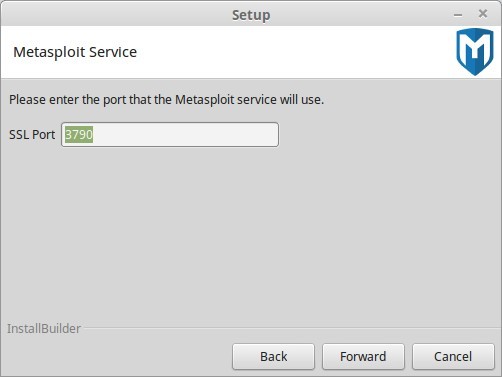
FIGURE 6
The next screen, Figure 7, prompts you for your system's Fully Qualified Domain Name (FQDN). To find this, use the command “hostname” in a terminal. If you need to change it, edit the file “/etc/hostname” and set it the way you want it. To change it temporarily, use the command “sudo hostname name”, where name is your FQDN. Once you have filled in the information required, a certificate will be made with the information you entered. Click “Forward” when done.
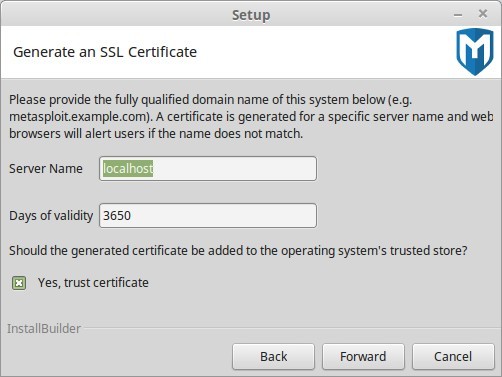
FIGURE 7
You should be notified, as in Figure 8, that Metasploit is now ready to be installed. Click “Forward” to start the installation.
The installation will begin at this point. Once completed, the window shown in Figure 8 will appear to show that the installation is complete.
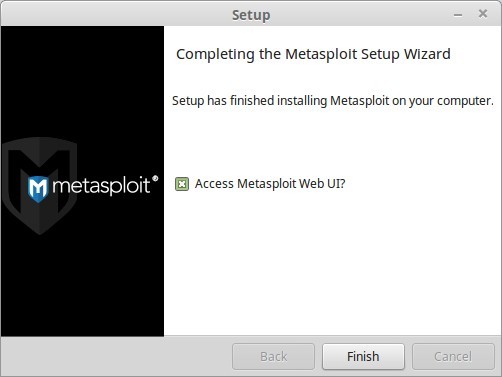
FIGURE 8
To access the webserver on your system, which was installed with Metasploit, leave the option for the Metasploit Web UI enabled on the last screen and click “Finish”. If not, go to the site “https://your_fqdn/:port_number”. The FQDN is the one you set during installation. The Port number was set as well. It is also possible to use “https://127.0.0.1:port_number” when attaching to it from the local PC. It may take about ten minutes before the web service becomes active by itself, so be patient and wait for it to start. After you can connect to the web service, you should see a site similar to Figure 9.
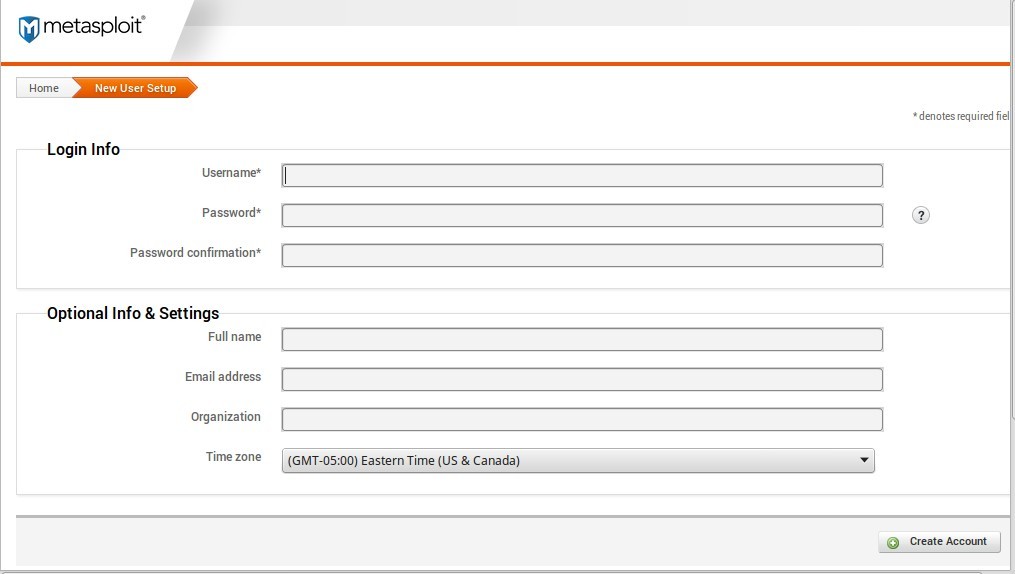
FIGURE 9
NOTE: The first time you connect to the metasploit system, you need to connect from the local host with the address of https://127.0.0.1:port_number to configure the system.
When the page loads, fill in the information to create a new account, then select the “Create Account” button in the lower right corner.
After creating the account, you need to then get a Product Key. You have a choice of Metasploit Pro (not free) and the Community Edition (free). Select the one you wish to use and the key should be e-mailed to the e-mail address you entered. Once you have the key, enter it in the web address.
At this point, you should see a screen similar to Figure 10. One thing to do right away is to select “Administration” at the top right and then select “Software Updates”. Perform any updates you need and let the services restart.
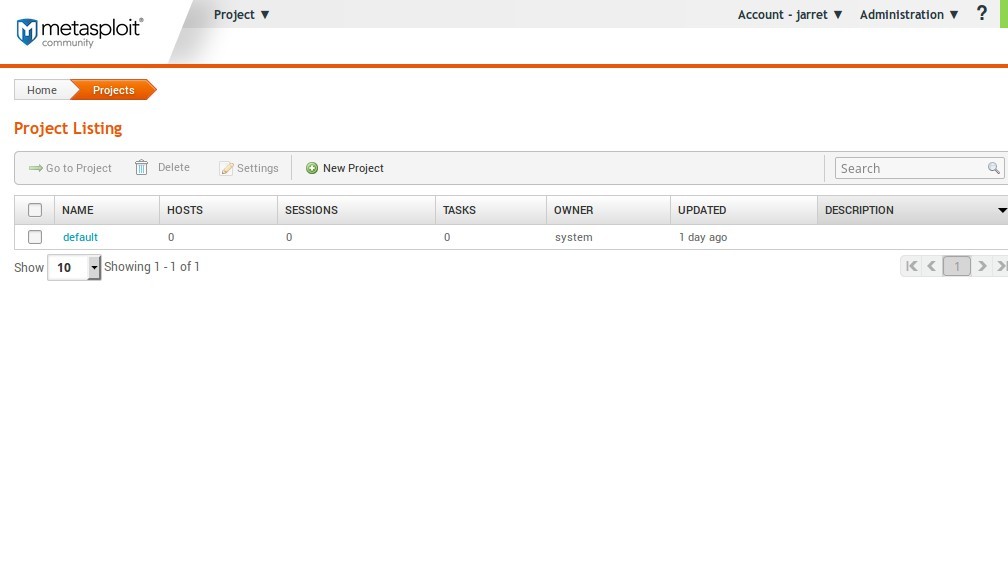
FIGURE 10
Now that Metasploit is installed, let's do a test by putting the program to work.
Open a terminal and type “sudo msfconsole”. Enter the password when prompted.
NOTE: It is imperative to run “msfconsole” as root to get control of the Network Interface Card (NIC).
It can sometimes take some time for the Metasploit Framework Console, which is shown in Figure 11. The main screen shown is a random one when starting. Your screen most likely will be different, but you are looking for the “msf >” prompt.
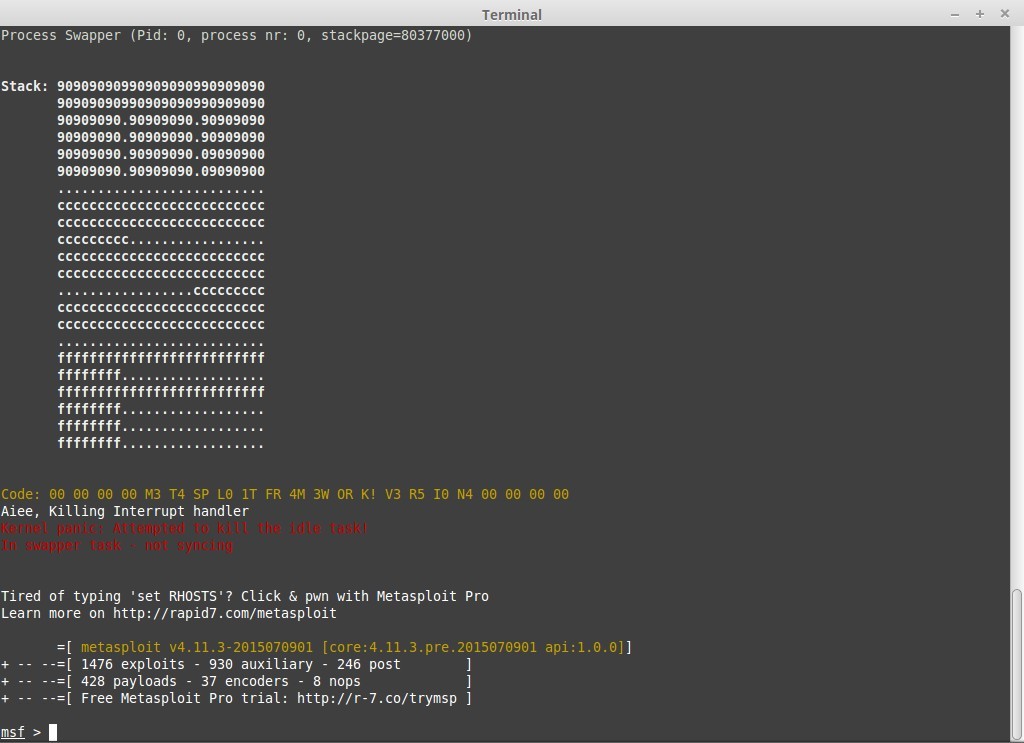
FIGURE 11
Once you see the “msf >” prompt, you are ready to begin. In the example, we will scan a network for all available systems (those powered on). For a wireless network this includes any devices connected to the Wireless LAN, such as Android devices. To start the scanning process, the “msfconsole” needs to load the necessary commands. So, the command is “use auxiliary/scanner/discovery/arp_sweep”.
Once loaded, a new prompt appears, “ msf auxiliary(arp_sweep) >”.
Use the command “show options” to see what is required when using this command set. You should see something like that shown in Figure 12.
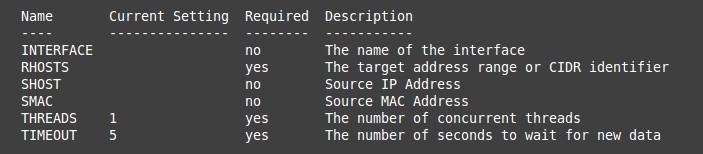
FIGURE 12
There are only three options required to be set, and two of those are already set to defaults. The main item to set is RHOSTS. The RHOSTS option lets “msfconsole” know which remote host addresses to scan. On my network, I want to scan all addresses from 192.168.2.1 to 192.168.2.254. To set this option, I use the command “set RHOSTS 192.168.2.1-254”. Once you press ENTER, type in the command “show options” and the RHOSTS setting should be changed. You may also want to specify the Network Interface. This is good practice in case you are performing tests from a system with two NICs. So, I type “set INTERFACE wlan0”.
Check the name of your NIC by typing the command in another terminal, “ifconfig”, and find your NIC. The THREADS should usually be between 20 and 25. Change the THREADS with the command “set THREADS 20”. Also, change the TIMEOUT with “set TIMEOUT 1”. Type “show options” and you should see something similar to Figure 13.
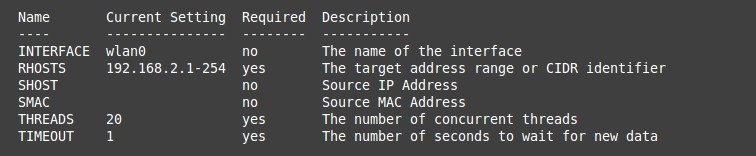
FIGURE 13
To start the scan, type “run” at the command prompt. A listing should appear showing devices on the specified network. My network is shown in Figure 14. Notice that in some cases, Metasploit also detects the NIC manufacturer as well.
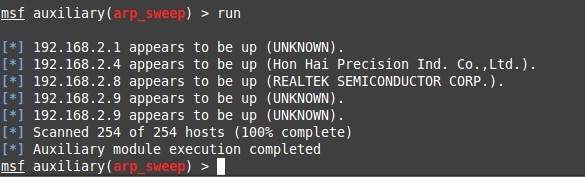
FIGURE 14
The device at 192.168.2.1 is my gateway which is a Belkin router. The device at address 192.168.2.9 is an Android device connect to the Wireless LAN. To close the msfconsole, type “exit” and press ENTER.
Metasploit is a penetration tool used to test vulnerabilities on systems in a network. Weak areas on the network are found so you can fix the security issues before a hacker can find them and exploit them.
Metasploit can be found at http://downloads.metasploit.com/data/releases/metasploit-latest-linux-installer.run. Once downloaded, you need to give it executable priveleges. You can then install it by running it as root with the command “sudo ./metasploit-latest-linux-installer.run”.
NOTE: You can also download Metasploit from http://www.rapid7.com/products/metasploit/download.jsp and receive the product key as well.
The screen should appear like Figure 1. To continue with the install, click the “Forward” button.
FIGURE 1
Next, look over the License Agreement, as shown in Figure 2, and select “I accept the agreement” and then click the “Forward” button.
FIGURE 2
The next window allows you to set the destination folder for the installation. The default is /opt/metasploit as seen in Figure 3. Change it if needed or accept the default and then press the “Forward” button.
FIGURE 3
The next screen prompts you to allow Metasploit to be run as a service. The service will automatically start when the system loads. Select “Yes” to accept the program to be run as a service or “No” if you want to start it manually. To start the service manually, type “sudo service metasploit start” in a terminal. Once done, select “Forward” to continue.
FIGURE 4
The next window alerts you to disable any Antivirus software and Firewall applications. The window is seen in Figure 5. Click the “Forward” button when you have read over the information.
FIGURE 5
The next screen prompts you to enter an SSL Port for metasploit to use. The default is 3790 as shown in Figure 6. Set the port number as you desire and click the “Forward” button.
FIGURE 6
The next screen, Figure 7, prompts you for your system's Fully Qualified Domain Name (FQDN). To find this, use the command “hostname” in a terminal. If you need to change it, edit the file “/etc/hostname” and set it the way you want it. To change it temporarily, use the command “sudo hostname name”, where name is your FQDN. Once you have filled in the information required, a certificate will be made with the information you entered. Click “Forward” when done.
FIGURE 7
You should be notified, as in Figure 8, that Metasploit is now ready to be installed. Click “Forward” to start the installation.
The installation will begin at this point. Once completed, the window shown in Figure 8 will appear to show that the installation is complete.
FIGURE 8
To access the webserver on your system, which was installed with Metasploit, leave the option for the Metasploit Web UI enabled on the last screen and click “Finish”. If not, go to the site “https://your_fqdn/:port_number”. The FQDN is the one you set during installation. The Port number was set as well. It is also possible to use “https://127.0.0.1:port_number” when attaching to it from the local PC. It may take about ten minutes before the web service becomes active by itself, so be patient and wait for it to start. After you can connect to the web service, you should see a site similar to Figure 9.
FIGURE 9
NOTE: The first time you connect to the metasploit system, you need to connect from the local host with the address of https://127.0.0.1:port_number to configure the system.
When the page loads, fill in the information to create a new account, then select the “Create Account” button in the lower right corner.
After creating the account, you need to then get a Product Key. You have a choice of Metasploit Pro (not free) and the Community Edition (free). Select the one you wish to use and the key should be e-mailed to the e-mail address you entered. Once you have the key, enter it in the web address.
At this point, you should see a screen similar to Figure 10. One thing to do right away is to select “Administration” at the top right and then select “Software Updates”. Perform any updates you need and let the services restart.
FIGURE 10
Now that Metasploit is installed, let's do a test by putting the program to work.
Open a terminal and type “sudo msfconsole”. Enter the password when prompted.
NOTE: It is imperative to run “msfconsole” as root to get control of the Network Interface Card (NIC).
It can sometimes take some time for the Metasploit Framework Console, which is shown in Figure 11. The main screen shown is a random one when starting. Your screen most likely will be different, but you are looking for the “msf >” prompt.
FIGURE 11
Once you see the “msf >” prompt, you are ready to begin. In the example, we will scan a network for all available systems (those powered on). For a wireless network this includes any devices connected to the Wireless LAN, such as Android devices. To start the scanning process, the “msfconsole” needs to load the necessary commands. So, the command is “use auxiliary/scanner/discovery/arp_sweep”.
Once loaded, a new prompt appears, “ msf auxiliary(arp_sweep) >”.
Use the command “show options” to see what is required when using this command set. You should see something like that shown in Figure 12.
FIGURE 12
There are only three options required to be set, and two of those are already set to defaults. The main item to set is RHOSTS. The RHOSTS option lets “msfconsole” know which remote host addresses to scan. On my network, I want to scan all addresses from 192.168.2.1 to 192.168.2.254. To set this option, I use the command “set RHOSTS 192.168.2.1-254”. Once you press ENTER, type in the command “show options” and the RHOSTS setting should be changed. You may also want to specify the Network Interface. This is good practice in case you are performing tests from a system with two NICs. So, I type “set INTERFACE wlan0”.
Check the name of your NIC by typing the command in another terminal, “ifconfig”, and find your NIC. The THREADS should usually be between 20 and 25. Change the THREADS with the command “set THREADS 20”. Also, change the TIMEOUT with “set TIMEOUT 1”. Type “show options” and you should see something similar to Figure 13.
FIGURE 13
To start the scan, type “run” at the command prompt. A listing should appear showing devices on the specified network. My network is shown in Figure 14. Notice that in some cases, Metasploit also detects the NIC manufacturer as well.
FIGURE 14
The device at 192.168.2.1 is my gateway which is a Belkin router. The device at address 192.168.2.9 is an Android device connect to the Wireless LAN. To close the msfconsole, type “exit” and press ENTER.


